Yubikeys Lakewood Ranch
How to use Yubikeys to protect accounts in Lakewood Ranch
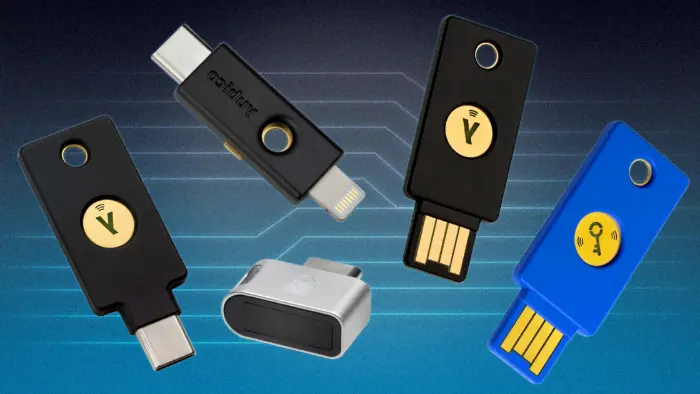
S3DA suggests that clients use a hardware key, such as a Yubikey, to protect important accounts connected to the internet.
YubiKeys are small, physical security keys that can be used to add an extra layer of security to your online accounts. They work by generating one-time passwords (OTPs) that are used to authenticate your identity when you log in. Other brands of hardware keys exist.
YubiKeys offer a number of benefits over other forms of two-factor authentication (2FA), such as SMS or push notifications. These benefits include:
- Stronger security: YubiKeys are more resistant to phishing attacks than other forms of 2FA. This is because they require physical possession of the key in order to generate an OTP.
- More convenient: YubiKeys can be used with any device that has a USB port, so you don't need to worry about carrying around a separate device or having to rely on your phone's battery life. S3DA likes that Yubikeys offers different port options such as USB-A and USB-C.
- More versatile: YubiKeys can be used with a wide range of online services, including Google, Facebook, Twitter, and GoDaddy.
- Prevents account takeovers: YubiKeys make it much more difficult for attackers to take over your accounts, even if they have your username and password. This is because they would also need to physically steal your YubiKey.
- Protects against phishing attacks: YubiKeys are immune to phishing attacks, which are a common way for attackers to steal login credentials. This is because YubiKeys require physical interaction with the device in order to generate an OTP.
- Increases user productivity: YubiKeys can help to increase user productivity by making it easier and faster to log in to accounts. This is because users don't have to remember multiple passwords or wait for SMS messages or push notifications.
Overall, YubiKeys are a valuable tool for anyone who wants to improve the security of their online accounts. They're easy to use, affordable, and offer a number of security benefits. If you're looking for a way to add an extra layer of security to your online accounts, a YubiKey is a great option. They're easy to use, affordable, and offer a number of security benefits.
S3DA strongly recommends the use of at least two keys and preferably three keys. Why?
- Redundancy: If your primary hardware key is lost, stolen, or stops working, having a backup key ensures you can still access your accounts and systems without interruption. It provides a failsafe mechanism and prevents being locked out of your accounts. Keep in mind that there is no "locksmith" or "help desk" should you lose a hardware key. If you only use one to secure an account, you will lose access to that account.
- Convenience: Having multiple backup YubiKeys allows you to keep them in different physical locations. For example, you can store one at home and another in a secure location, such as a safe or a trusted family member's house. This way, even if one YubiKey is inaccessible, you still have access to a backup. Three keys allows you to keep one in your house, one in your safe in your house, and one in a separate location such as work or a trusted family member.
- Travel and mobility: If you frequently travel or use multiple devices, having backup hardware key can be particularly useful. You can keep a key with you while traveling and have additional ones stored securely at your home or office.
- Shared accounts: In some cases, multiple individuals might require access to the same account or system. Each person can have their own YubiKey, and having backup hardware key ensures that multiple individuals can access the account even if their primary YubiKey is not available.
Risks Associated with Hardware Security Keys
Yubikeys are very secure devices, but there are a few risks to be aware of:
Phishing attacks: Phishing attacks are attempts to trick users into revealing their personal information or clicking on malicious links. Attackers can create phishing emails or websites that look like legitimate Yubico websites or login pages. If a user falls for a phishing attack and enters their YubiKey credentials, the attacker could steal their account.
Backup: It's important to have a backup plan in place in case your YubiKey is lost or damaged. Some services allow you to set up multiple YubiKeys or provide backup authentication methods, such as one-time codes or backup codes.
Dependency on a Single Device: Relying solely on a single YubiKey can lead to issues if the device becomes unavailable for any reason (e.g., loss, damage). Having backup authentication methods or multiple YubiKeys is advisable.
Fake Yubikeys: There have been cases of counterfeit Yubikeys being sold online. These devices may look like real Yubikeys, but they may not be secure. In some cases, fake Yubikeys have been used to steal user credentials or install malware on users' computers.
Physical loss or theft: If a YubiKey is lost or stolen, an attacker could use it to gain access to the user's accounts. It is important to keep Yubikeys in a safe place and to have a backup authentication method in case the YubiKey is lost or stolen.
Cost: YubiKeys can be relatively expensive compared to other forms of 2FA or authentication methods, which could be a consideration for individuals or organizations on a tight budget.
Other risks:
- NFC sniffing: NFC-enabled Yubikeys can be vulnerable to sniffing attacks, where an attacker could use a device to intercept the NFC signal and steal the user's credentials. However, this type of attack is relatively difficult to carry out and requires the attacker to be very close to the victim.
- Denial of service attacks: An attacker could launch a denial of service attack against a user by repeatedly requesting authentication codes from their YubiKey. This could prevent the user from logging into their accounts. However, most Yubikeys have a built-in feature that limits the number of authentication requests that can be made in a certain period of time.
Overall, Yubikeys are very secure devices, but it is important to be aware of the risks and to take steps to mitigate them.
Here are some tips for using Yubikeys safely:
- Only buy Yubikeys from trusted retailers.
- Keep your YubiKey in a safe place.
- Have a backup authentication method in case your YubiKey is lost or stolen.
- Keep your YubiKey up to date with the latest security updates.
- Be aware of phishing attacks and other social engineering scams.
If you are concerned about the risks of using a YubiKey, you can also use a different type of two-factor authentication device, such as an authenticator app on your smartphone. However, Yubikeys are generally considered to be more secure than authenticator apps.
Add Hardware Security Key - Guides for Lakewood Ranch Clients
The following links will help you set up a physical security key with your accounts. Contact S3DA if you need additional help. We can provide you with a flat rate quote to help you configure your business and personal accounts with hardware security keys.
Pros and Cons of Yubikeys vs Authenticator Software Apps
YubiKey:
- YubiKeys provide robust security and are considered superior to authenticator apps. They support the WebAuthn protocol, which significantly enhances security against phishing attacks.
- YubiKeys are highly secure due to their hardware-based design. The secret credentials stored on a YubiKey are nearly impossible to extract and clone.
- YubiKeys work across various platforms and devices. They can be used on both computers and mobile devices.
- YubiKeys are durable and less likely to be damaged or stolen compared to phones. They withstand wear and tear.
- If your phone breaks or you get a new one, you can effortlessly use the YubiKey on the new device. A single YubiKey can be moved between your own devices.
- Yubikeys provide an easier backup in that they are relatively less expensive to buy multiples of. If one is lost, damaged, or stolen, backups can be stored in multiple locations. Most people are unlikely to keep a backup phone. A new phone can take time to source.
Authenticator Apps
- Can be more convenient since most people will carry a phone.
- Only one device to carry and most people will carry a phone.
About S3DA Lakewood Ranch
S3DA is an elite Lakewood Ranch website design and website SEO agency. We are expert at achieving Google Page 1 search engine results by combining website design and Google SEO without using paid click marketing campaigns.
Our clients include small businesses, corporate departments, and not-for-profits.Let us show you how our clients' websites compare to the competition in Google web search. You will clearly see that S3DA is the best website design agency for Lakewood Ranch websites.